Discover the best legal ethical hacking tools beginners should master in 2026. Learn Nmap, Metasploit, Burp Suite, and more with career insights.
In This Article
Introduction: Why Ethical Hacking Tools Matter in 2025
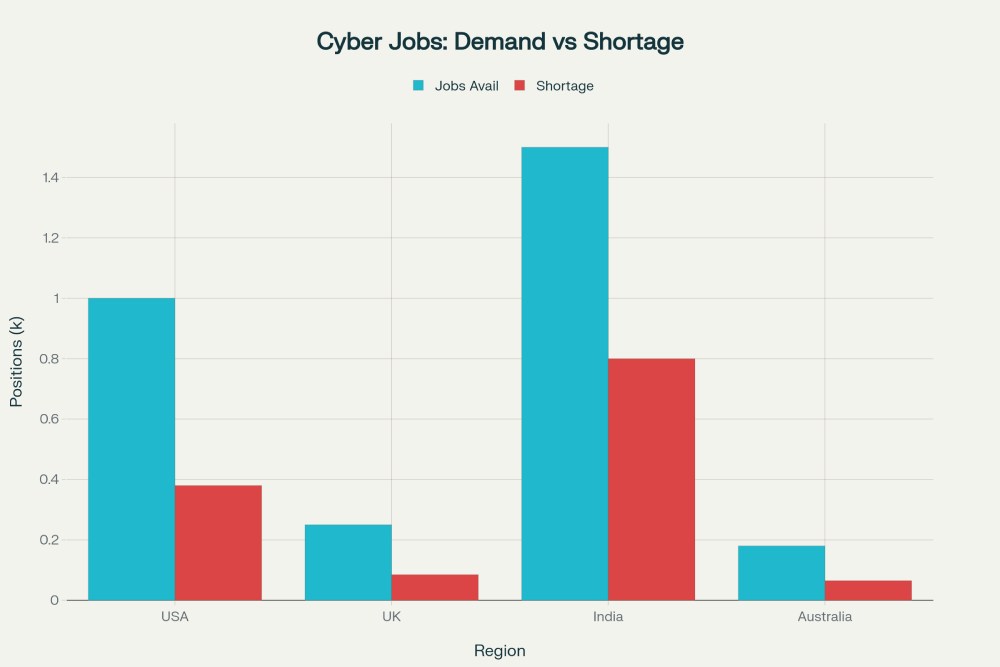
Envision yourself on the cusp of a $250 billion cybersecurity market where the need for qualified workers is outstripping supply. This is what the world’s workers will have to deal with in 2026. The world of cybersecurity has changed a lot, and with more than a million open positions, mastering ethical hacking tools for beginners is now a smart career move, not just a fun pastime.
But here’s the problem: newbies sometimes feel stuck because there are so many tools to choose from. What ones really matter? Which tools can help you start a real career? This complete guide cuts through the noise and shows the finest legal hacking tools for 2026 that everyone who wants to work in cybersecurity should know how to use to be competitive in this fast-growing area.
What Is Ethical Hacking & Why It Matters in 2026
Ethical hacking, which is sometimes called penetration testing or white-hat hacking, is a legal and allowed way for qualified security professionals to check out computer systems, networks, and apps. Ethical hackers look for holes before cybercriminals may use them for their own gain, while malevolent hackers take advantage of them for their own gain.
In 2026, the importance of ethical hacking will have reached a turning point. Cyber dangers are at an all-time high for businesses throughout the world. These threats range from AI-powered ransomware to complex phishing campaigns that may take down entire business networks. The Data Security Council of India said that in 2024, India found 369 million malware incidents on 8.44 million installations. This huge rise in attacks has made it necessary to hire certified professionals very away, and they are willing to pay more for their services.
Important Differences Between Ethical Hacking and Illegal Hacking
The difference between ethical and criminal hacking isn’t just a matter of words; it’s the line that separates a successful career worth six figures from federal prosecution. To get real cybersecurity jobs, you need to know about these differences.
Ethical hackers only work with clear written permission. Before any penetration test, vulnerability assessment, or security audit can commence, both parties must sign a contract that clearly states which systems can be evaluated, which testing methods are allowed, and which are not. This requirement for authorization is the legal basis for the profession.
Ethical hackers follow the rules for responsible disclosure. When vulnerabilities are found, they are disclosed to the organization’s security staff in private, along with full documentation and suggestions for fixing the problem. They are never used for profit or to disgrace the company in public. The OWASP Code of Ethics and other industry standards spell out this professional duty.
Ethical hackers keep things private and honest. The data collected during penetration tests is kept completely private. Ethical hackers never steal data, look at private information that isn’t part of the test, or keep backdoor access after the test is over. Clients pay extra for this promise of trustworthiness.
Hackers that break the law do so without permission, for their own gain, and to hurt others. Unauthorized access is against the law in the US and most other nations. The Computer Fraud and Abuse Act (CFAA) is one of these laws. The repercussions are jail time, big fines, and criminal charges.
Legal Certifications and Knowledge of Compliance
If you want to learn how to use penetration testing tools and ethical hacking abilities without getting industry-recognized qualifications, you could be putting your career at risk. More and more, companies that hire cybersecurity professionals want to see proof of their knowledge and ethical commitment.
The Offensive Security Certified Professional (OSCP) is the best certification for anyone who do penetration testing. The CEH is more theoretical, but the OSCP demands passing a hard 24-hour practical test in which applicants must find and exploit real vulnerabilities in a live lab setting. To get ready for the OSCP, you usually need to study and practice for 6 to 12 months. In India, professionals with an OSCP certification may expect to make between ₹6,00,000 and ₹12,00,000 a year, and in the US, they can expect to make between $100,000 and $190,000 a year.
Many organizations require CompTIA Security+ as a basic credential before hiring someone for a security job. This certification covers more than only ethical hacking when it comes to IT security, yet it is still useful for developing a strong security base.
Ethical hackers must also know about the laws and rules that apply to penetration tests before they start. HIPAA compliance is for healthcare businesses, PCI-DSS is for payment card data, GDPR is for protecting the data of European citizens, and SOC 2 regulations are for service providers. Every certification shows that you know not only how to use the tools, but also the legal and moral duties that come with working in cybersecurity.
The Best Ethical Hacking Tools for Beginners (2026 Edition)
Tools for Network Scanning and Reconnaissance
Every novice should learn how to use Nmap (Network Mapper), which is the most basic network scanning tool. This free tool examines networks to find active hosts, open ports, running services, and operating systems by fingerprinting. Nmap is powerful because it can do a lot of different things. For example, it can do basic TCP connect scans for beginners, complex SYN scans for stealth, OS detection, service version identification, and custom scripts through the Nmap Scripting Engine (NSE).
Why novices need it: Port scanning is the first thing you need to do for any penetration test. Nmap answers the most basic question: “What services are running on this network?” Learning Nmap gives you the basic knowledge you need to understand network reconnaissance and opens the door to mastering more advanced penetration testing tools.
Level of difficulty: Easy to use with a command-line interface
License: Free and open source
Nmap proficiency is a skill that all security analysts should have; therefore, it can help your career.
Nessus became the standard tool for finding security holes in software. Nmap finds open ports and services, but Nessus goes farther. It examines those services against a database of more than 12,000 known vulnerabilities and misconfigurations. Nessus checks anything with plugins that are updated regularly, finds missing security patches, finds weak encryption methods, and gives each vulnerability a CVSS severity level.
Why novices need it: Companies can’t safeguard things they can’t see. Nessus takes raw network data and turns it into useful information by systematically finding and measuring security holes. The free version has enough features for learning. The professional editions add authenticated scanning and more comprehensive compliance testing.
Difficulty: Easy to use for beginners with a web-based interface
License: There is a free version, and the professional version costs $2,600 per year per scanner.
Career benefit: Most job postings for vulnerability analysts list experience with Nessus as a requirement.
Important Links:
If you are looking for the World’s Greatest Wealth Books, Help You Earn 1 Cent Per Second

Tools for Securing Web Applications
The Burp Suite Community Edition is a full set of tools for evaluating the security of online applications, and it doesn’t cost $400 a month as the professional edition does. This open-source proxy stops HTTP and HTTPS traffic so that testers can change requests before they get to the server, look closely at server responses, and find common online vulnerabilities.
Why novices need it: Burp Suite shows how assaults on current web applications really work. You may learn how SQL injection works by actually doing the attack instead of just reading about it in books. The proxy part shows you exactly what data your browser sends with each request.
Level of difficulty: Intermediate (you need to know about HTTP and web protocols)
License: The Community Edition is free, however the Professional Edition costs $399 a month.
Burp Suite knowledge is necessary for online security and bug bounty jobs, which is good for your career.
Many professional penetration testers utilize OWASP ZAP (Zed Attack Proxy) as a free, open-source alternative to Burp Suite. They use it combined with commercial products. ZAP can automatically scan websites for security holes, scan them passively without assaulting them, scan them with a login page for testing, and work with CI/CD pipelines for ongoing security testing.
Why beginners need it: ZAP is great for students and beginners because it is easy to use. The Open Web Application Security Project (OWASP), which is the best source of information about web application security, maintains and documents the tool.
Level of difficulty: easy for beginners
License: Open-source and free
Career benefit: Shows initiative by employing technologies that are mainstream in the business
Nikto is a tool that scans web servers for security issues. It works with Burp Suite and ZAP, which are more general tools. Nikto searches quickly to find files that could be dangerous, old versions of server software, common misconfigurations, and more than 6,700 files and scripts that could be dangerous in its vulnerability database.
Why beginners should use it: Nikto is good at finding things that bigger tools could miss. The tool is light, quick, and great for getting to know a web server for the first time. Its command-line interface teaches newcomers how to undertake penetration testing.
Level of difficulty: easy for beginners
License: Open-source and free
Career benefit: Shows that you know how to use specialist reconnaissance tools
Tools for testing and breaking passwords
Kali Linux comes with John the Ripper by default, and it is still the best tool for cracking passwords. This open-source tool can work with many different hash formats, such as MD5, SHA, and bcrypt. It can also use different types of attacks, such as dictionary attacks that use wordlists, brute-force attacks that try every possible combination of characters, and rule-based attacks that change dictionary words according to rules that can be changed.
Why beginners need it: To stay safe online, you need to know how weak passwords are. You can understand why password managers, entropy, and complexity requirements are important by utilizing John the Ripper in labs. The tool shows why people have trouble with passwords and how important it is to have secure authentication systems.
Level of difficulty: Intermediate (you need to know how hash formats work and how attacks work)
License: Free and open-source
Career benefit: Knowing how to keep passwords safe is useful in all cybersecurity jobs.
Hashcat is the best tool for cracking passwords since it uses GPU acceleration to crack passwords far faster than CPU-based programs. A modern GPU can do billions of hash calculations per second, which makes cracking circumstances that were once unthinkable viable.
Hashcat is important for beginners since it teaches them about password entropy and why salting is important. Watching how quickly hash cracking works makes it clear why security experts recommend lengthy, complicated passwords and why companies have password standards.
Level of difficulty: Intermediate to Advanced
License: Open source and free
Career benefit: Candidates for senior penetration testing roles stand out since they have advanced expertise.
Important Links:
If you are looking for the World’s Greatest Wealth Books, Help You Earn 1 Cent Per Second

OSINT and tools for gathering information
Maltego is like a Swiss Army knife for obtaining open-source intelligence (OSINT). This desktop program combines more than 58 public data sources, such as Google Maps geocoding, AlienVault OTX threat intelligence, blockchain data, VirusTotal malware analysis, and CrowdStrike intelligence feeds. Maltego shows how entities (people, corporations, email addresses, domains) are connected by using interactive graphs. This makes patterns that wouldn’t show up in raw data.
OSINT is the “passive” reconnaissance phase, which means you obtain information without touching the target’s systems. Maltego shows how much information is available to the public and explains why data privacy is important. Compared to command-line OSINT tools, the visual interface makes learning easy.
Level of difficulty: easy for beginners
License: The Community Edition is free, but there are paid Premium versions.
OSINT abilities are useful in a lot of different jobs, such as threat intelligence, incident response, and investigations.
Recon-ng is a command-line OSINT framework with more than 58 modular plugins for things like domain reconnaissance, IP geolocation, DNS enumeration, SSL certificate analysis, breach database searches, and gathering threat intelligence. The modular design lets new users choose various OSINT tasks without having to learn everything about the application at once.
Why novices need it: Recon-ng explains command-line OSINT operations and shows how to combine data from different sources to make complete target profiles. The tool shows that professional reconnaissance depends more on persistence and putting together information than on advanced technology.
Level of difficulty: Intermediate (command-line based)
License: Open source and free
Career benefit: Knowing OSINT sets good penetration testers apart from script-runners.
SpiderFoot has more than 200 data collecting modules that do OSINT automatically. This program collects information about target domains, IP addresses, email addresses, organizations, and people in a methodical way from a variety of sources, such as DNS records, search engines, social media, breach databases, and threat intelligence platforms.
Why beginners need it: SpiderFoot’s automation saves them hours of study. Beginners can spend less time doing the same searches over and again and more time figuring out what the results mean, which speeds up their learning of reconnaissance methods.
Level of difficulty: easy for beginners
License: Open-source and free
Career benefit: Shows that you have an automation and efficiency attitude that businesses value
Tools for testing wireless security
Aircrack-ng is a complete wireless security framework that includes Airmon-ng (for putting wireless adapters in monitor mode), Airodump-ng (for capturing wireless traffic and encryption handshakes), Aireplay-ng (for injection attacks to speed up data collection), and Aircrack-ng itself (for recovering WEP and WPA/WPA2 encryption keys).
Why beginners need it: It’s becoming more and more important to know about wireless security. Aircrack-ng highlights why businesses can’t ignore WiFi security and why enhancements to WPA2 are important. Students can learn about real security concepts by doing hands-on wireless testing at home with regular equipment.
Level of difficulty: Intermediate (you need to know about wireless protocols and encryption)
License: Open source and free
Career benefit: Wireless penetration testing is a specialist field that pays more.
Kismet can find wifi networks, sniff them out, and tell you if someone is trying to break in. This tool finds wireless networks, finds hidden SSIDs, finds rogue access points, finds devices that shouldn’t be there, and keeps a record of all wireless traffic for later analysis.
Why beginners need it: Kismet explains how to passively scan wireless networks without assaulting them directly. Before doing active assaults in a proper penetration testing process, you need to know how networks are set up and how devices work.
Level of Difficulty: Intermediate
License: Free and open-source
Career benefit: Shows a thorough reconnaissance technique that is respected in professional evaluations
The Metasploit Framework is the standard exploitation platform in the industry. It has hundreds of ready-to-use exploits, auxiliary modules for scanning and enumeration, payload generators, and tools for after exploitation. The best thing about Metasploit is that it is modular, thus each exploit, payload, and auxiliary module works well with the others.
Penetration Testing Frameworks
The Meterpreter payload is the most powerful part of Metasploit. After taking advantage of a flaw, Meterpreter gives you an interactive shell right in the target’s memory (not writing to disk). This lets you transfer files, steal credentials, gain more privileges, find out more about the system, and move laterally—all without being seen.
Why novices should use it: Metasploit changes the way penetration testing works. Instead than developing each exploit code, you choose pre-made modules, set targets, and carry out full attacks. This lets beginners learn about exploitation and attack chains without needing to know a lot about programming.
Level of difficulty: Intermediate to Advanced
License: Free and open-source (Community Edition; Commercial Pro version available)
Career benefit: Almost every job description for a penetration tester includes experience with Metasploit.
Kali Linux is the best operating system for penetration testing because it comes with over 600 security tools, including all of the apps described above. Kali is based on Debian Linux and comes with everything you need to get started, so you don’t have to deal with the hassle of installing it.
Why beginners need it: Instead of installing a lot of different tools and keeping track of their dependencies, beginners can download Kali as a virtual machine and start practicing right away. The standardized environment makes sure that all the tools work properly, and the full toolbox lets you learn everything from basic network scanning to complex exploitation.
Difficulty: Easy for beginners to use pre-installed tools; Intermediate for people who know how to use the Linux command line
License: Open source and free
If you want to work in cybersecurity, you pretty much have to know how to use Kali.
Network Monitoring and Packet Analysis tools
Wireshark captures and analyzes network packets in real time. It shows detailed information about protocols, application-level data, and network flow statistics. This free utility can record traffic from any network interface and let you look at the packets you caught later
Why beginners need it: Knowing how network protocols function is an important part of being safe online. Wireshark makes protocols real by letting you view exactly what data your apps send, learn how protocols talk to each other, and spot strange patterns in traffic. Beginners regularly find credentials sent in cleartext, which shows how important encryption is.
Level of difficulty: Easy for basic packet capture; Intermediate for thorough protocol analysis
License: Free and open source
Network analysis skills set candidates apart for security jobs, which is good for their careers.
How to Set Up Your Ethical Hacking Lab
To learn how to use ethical hacking tools, you need to practice with them. The best place to do this is in a controlled lab that you entirely control. Virtual machines are the best platform because you can set up test environments that are vulnerable, carry out real attacks, and break things without any consequences.
Recommended lab setup:
Virtual Box or VMware Workstation (both free) should host your virtual computers in the lab. Get Kali Linux to use as your attack computer. Set up purposely susceptible target machines like DVWA (Damn susceptible Web Application), Metasploitable (deliberately vulnerable Linux), or WebGoat (vulnerable web application from OWASP). Make a separate virtual network for your lab traffic so it doesn’t affect production systems. You can practice securely in this separate lab setting and learn skills that you can use in your job.
HackTheBox, TryHackMe, and PentesterLab are some of the platforms that offer pre-configured labs that you can access through your online browser. This means you don’t need any local infrastructure. These platforms include guided learning courses for beginners, capture-the-flag competitions for skill improvement, and real-world scenario simulations.
Also Read:
5 Low-Cost Web Hosting Services
How to Earn 1 Cent per Second: Money Attraction Laws and Rules
From Vibe Coding to Intent-Driven Software
Career Opportunities and Salary Potential
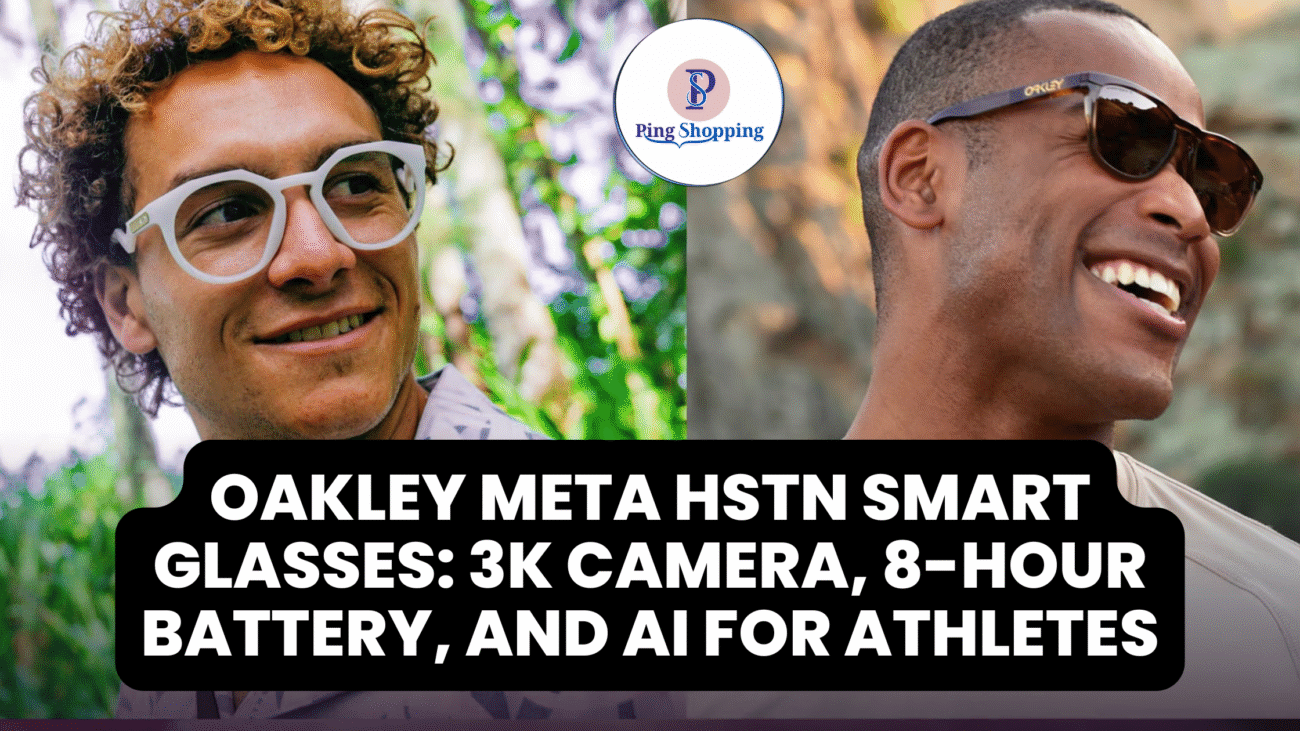
Compared to most other computer sectors, a career in cybersecurity offers great pay and employment security. Entry-level cybersecurity jobs in the US pay between $65,000 and $78,000 a year to people who have the right qualifications and skills. Mid-level jobs (3–7 years of experience) pay between $100,000 and $149,500 a year. Senior penetration testers and security architects make between $150,000 and $250,000 or more.
International markets also have strong pay. Cybersecurity professionals in the UK make between £50,000 and £92,600 a year, depending on how much experience they have. Cybersecurity specialists in Australia make between $76,500 and $127,000 or more, depending on their level of experience.

END OF THE ARTICLE:
If you really want to work in cybersecurity in 2026, this isn’t the end of your journey. This guide’s tools and information are only the start of your adventure. In the realm of cybersecurity, people who combine academic knowledge with practical skills and a commitment to lifelong learning are rewarded.
Frequently Asked Questions
Can I learn ethical hacking without programming knowledge?
Yes, beginners can use network scanning, enumeration, and passive reconnaissance tools that don’t require any programming. But for intermediate and advanced penetration testing, knowing how to use Python scripts and the command line is helpful. Along with tools for ethical hacking, start studying the basics of the Linux command line and Python.
Is ethical hacking legal?
When system owners give you clear written authorization, ethical hacking is completely lawful. Before you test any system, be sure you have the right permission. If you operate without permission, you are breaking the Computer Fraud and Abuse Act and similar laws in other countries. This can lead to jail time and other criminal consequences.
How long does it take to become job-ready as an ethical hacker?
Most beginners can get entry-level cybersecurity certifications (CEH, CompTIA Security+) within 3–6 months and get junior roles within 6–12 months if they study hard (20+ hours a week). Most people need to study for 6 to 12 months before they can get their OSCP certification. But hands-on experience is more important than time invested; practicing in real situations is the best way to get better.
Which certification should I pursue first—CEH or OSCP?
CEH is the best place for novices to start. It covers 270 security themes in depth, has less requirements, and takes 3 to 6 months to get ready for. After getting your CEH and working as a penetration tester for one to two years, you should get your OSCP to learn more advanced skills and get better-paying jobs. Many successful professionals go on to get both certificates and the CISSP to become leaders.
Can I practice ethical hacking legally without paying for certifications?
Of course. You can learn a lot of skills for free by using HackTheBox, TryHackMe, CTF tournaments, susceptible apps like Metasploitable and DVWA, and online classes. You don’t have to pay for certification. But credentials speed up career growth and show employers that you are committed. The CEH and CompTIA Security+ certifications are great investments for your career.
Do I need a computer science degree to work in cybersecurity?
Not at all. Many successful cybersecurity experts originated from non-technical backgrounds, military IT, network management, or self-taught approaches. Certifications, real-world skills shown through projects, bug bounty findings, and security blog material are often more important than formal schooling. But in cybersecurity, you have to keep learning and improving your skills.
Which ethical hacking tool should I learn first?
Start with Nmap to scan your network, then move on to OWASP ZAP or Burp Suite Community to test web applications. These basic tools explain the basics of penetration testing. Once you know how to do reconnaissance and scanning, move on to Metasploit for exploitation and more advanced methods. This smooth process improves comprehension over time instead of overwhelming new learners.
“If you found this article helpful, share it with your circle and follow PingShopping on social media”